Cyber attacks and security breaches are always a part of every news headline. Hardly anyone can shield themselves against these illicit activities. Nowadays, both small businesses and mega-enterprises are susceptible to unexpected cyberattacks, regardless of how strong their defenses are.
Companies lose billions of dollars without a trace of the attackers. Even commoners fall victim to data exploitation, privacy breaches, cyberbullying attacks, and ransom threats. Moreover, these incidents are increasing as digital exposure and reliance on technology increase.
These facts mean that cybersecurity is a rapidly evolving and growing field. So aspirants have immense potential and scope for a successful career in this field. Their knowledge and services are vital to ensure the security of data, information, and individual privacy. As a result, most employers are vying for potential candidates to help them guard their databases and assets.
They are willing to pay desired salary packages and other fringe benefits. You can start with lucrative packages even with a primary technology-related degree. In short, the academic journey, time commitment, expenditure, and efforts in a cybersecurity career are all worth it.
An enriched experience and advanced qualifications like an MS degree in cyber security management will further multiply your career options.
With that in mind, the following sections explore some of the best choices to embark on an exciting career journey in cybersecurity.
- Cybersecurity risk analyst
Cybersecurity risk analysis is one of the most progressive career paths. These analysts are responsible for day-to-day security assessment activities. They keep track of security protocols and emerging cybersecurity threats and endeavor to enhance an organization’s resilience against cybercrimes and online attacks.
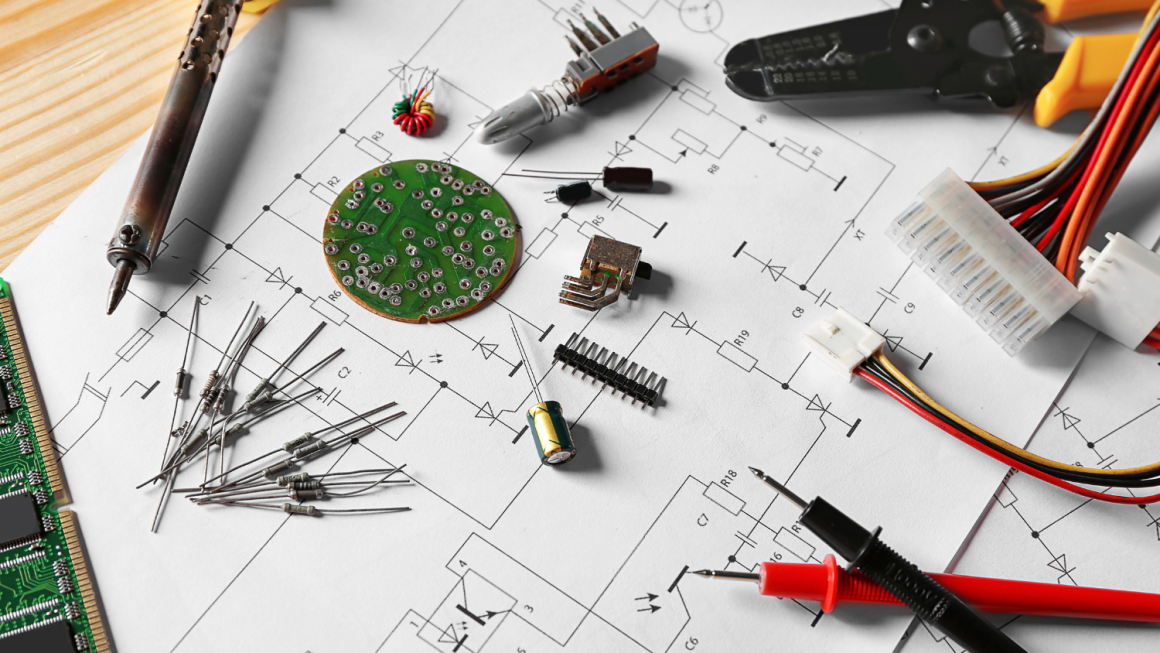
They plan, design, execute, and update security measures and protocols for hardware, networks, databases, servers, and operating systems. They also analyze and observe malware software, viruses, and hacking attacks and design suitable defensive mechanisms.
Since they have commendable analytical and research aptitude, organizations also use their skills to assess the potential of existing security measures, frameworks, and controls.
Organizations also seek their suggestions while developing cybersecurity policies or partnering for security agreements with third parties.
- Security Engineer
Security engineering is a mid-level career position, and a bachelor’s degree in cybersecurity or computer science can help you get started. But expertise in programming languages like java, C, C++, and python, is vital to perform the responsibilities of the post.
Many employers also value substantial knowledge of communication networks, networking protocols, cloud computing, and advanced certification courses like CISM, CISA, CISSP, and others. Nonetheless, security engineers assess security risks and test the efficacy of on-the-ground safeguarding measures.
They install intrusion detection systems, firewalls, and antiviruses to detect malicious activities at the right time. They also design, develop, and implement tools, services, frameworks, and methodologies to minimize security vulnerabilities.
In addition, security engineers also contribute to the decision-making and policies of an enterprise to strengthen the safety of networks, systems, and devices. These professionals endeavor day and night to keep data, networking systems, and devices from exploitation and illegal usage.
3. Chief information officer
Individuals with computer science, information technology, cybersecurity bachelor’s degree, and relevant experience reach the executive position of chief information officer. Many also pursue an MBA degree to strengthen their application for managerial positions.
So a chief information officer is a senior-level position in the information technology department of an organization. They mainly oversee and govern IT department operations, especially the security division. They coordinate with management and executives to identify the cyber security requirements of an organization. And for that, they plan, assist, direct, and lead all networking, computing, and security needs.
They are also on the frontlines to facilitate, manage, navigate, and implement technology and cybersecurity-related upgrades and protocols. In addition, they also engage in recruitment processes as part of the management board. And their focus is specific to the technical and cybersecurity team development.
4. Cybercrime analyst
Cybercrime analysts are detectives of the cyber world who cater to illicit virtual and digital attacks. They trace, investigate, and resolve cybercrimes and security breach incidents. Cybercrime analysts explore and collect digital evidence to solve a cybercrime issue.
These conduct extensive investigation operations and examine all access points, security measures, logs, search history, databases, malicious activities, and digital communication between devices.
They also use (ethical) hacking skills to trace, decode, and solve a breach attack. They use reverse hacking techniques to examine how hackers gained access and pinpoint security vulnerabilities.
Human resources are also part of their interrogation, along with their devices. In addition, they also help organizations recover from cyber-attacks. Recovery efforts may involve strengthening security parameters, recovering lost data, and repairing corrupted files and devices.
In a nutshell, their work is similar to forensic experts who investigate real-life cases and crimes. Only their domains are different.
5. Cryptographer
Cryptography is another progressive career direction in cybersecurity. It is a middle-level career position in an organization.
Specifically, cryptographers have a solid foundation in computer languages and information technology theories. They also have expert-level knowledge of encryption techniques and algorithms. Their mathematical, analytical, logical, and statistical expertise is also superb.
The combination of diverse skills, aptitude, and technical educational background raises their profile as data security specialists. And the demand for these exports is increasing as cybercrimes and terrorist attacks are commonplace. So cryptographers work in law enforcement agencies, technology hubs, business enterprises, governmental entities, and others.
Their primary duties include analyzing and decoding encrypted information and messages from terrorists and hackers. They develop complex security encryption techniques and passwords to protect confidential and sensitive data from unauthorized access, misuse, exploitation, and cybercrimes.
They also secure data communication between devices and networks via ciphering and deciphering techniques.
6. Ethical hacker
Ethical hackers or penetration testers have the same fundamental responsibilities as other cybersecurity experts; to safeguard data and prevent cybersecurity attacks. This career position is also valuable in the cybersecurity domain.
Organizations seek the services of ethical hackers to secure data and resources. As for the job responsibilities, ethical hackers track illicit hacking attacks and undo the damage. They utilize the same steps, strategies, and thought-processing as hackers to gain access to the networks and systems of an organization.
But their purpose is to test the effectiveness of security measures and protocols. Hence, they identify and examine security-related gaps and vulnerabilities in networks, hardware, software, and web applications.
Easy access and logging in through entry points and gateway systems mean security measures and protocols are not strong enough and need upgrades. So they implement necessary improvements and upgrades to block unauthorized intrusion and cybersecurity attacks.
Conclusion
Cybersecurity is developing at a rapid pace, and so are career opportunities. But you do not need a specific world-class degree to kick-start your career in cybersecurity. Any IT or computer science-related degree can help build a profile and gain the required skills and aptitude.
You can further expand your expertise and improve your knowledge base with certification courses, diplomas, or advanced degrees in cybersecurity. Many employers also value short training courses if candidates have a technology and computer studies background.
So go and explore the world of opportunities waiting for you.